Three Modern Quantitative Privacy Risk Models (Infographic)

All infographics are CC BY and you may use them in their existing format. You may also download the original pdf here. For commercial use, please contact us. Download PDF
A Taxonomy of Privacy (Infographic)
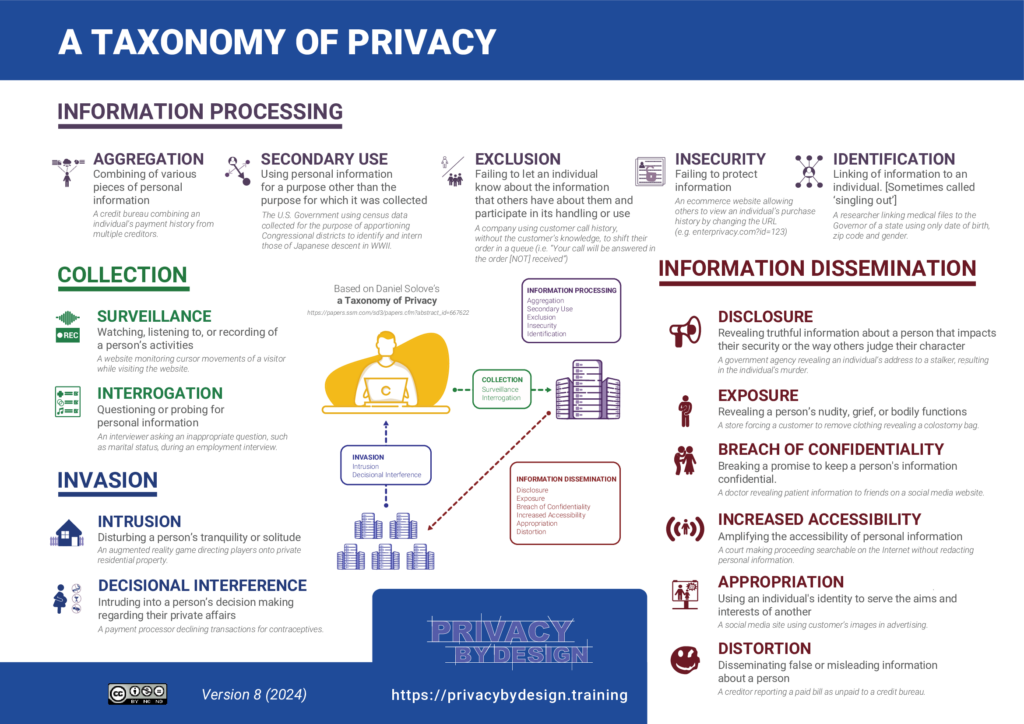
All infographics are CC BY and you may use them in their existing format. You may also download the original pdf here. For commercial use, please contact us. Download PDF
Strategies and Tactics (Infographic)

All infographics are CC BY and you may use them in their existing format. You may also download the original pdf here. For commercial use, please contact us. Download PDF
Strategic Privacy by Design Process (Infographic)

All infographics are CC BY and you may use them in their existing format. You may also download the original pdf here. For commercial use, please contact us. Download PDF
Models of Privacy Norms (Infographic)
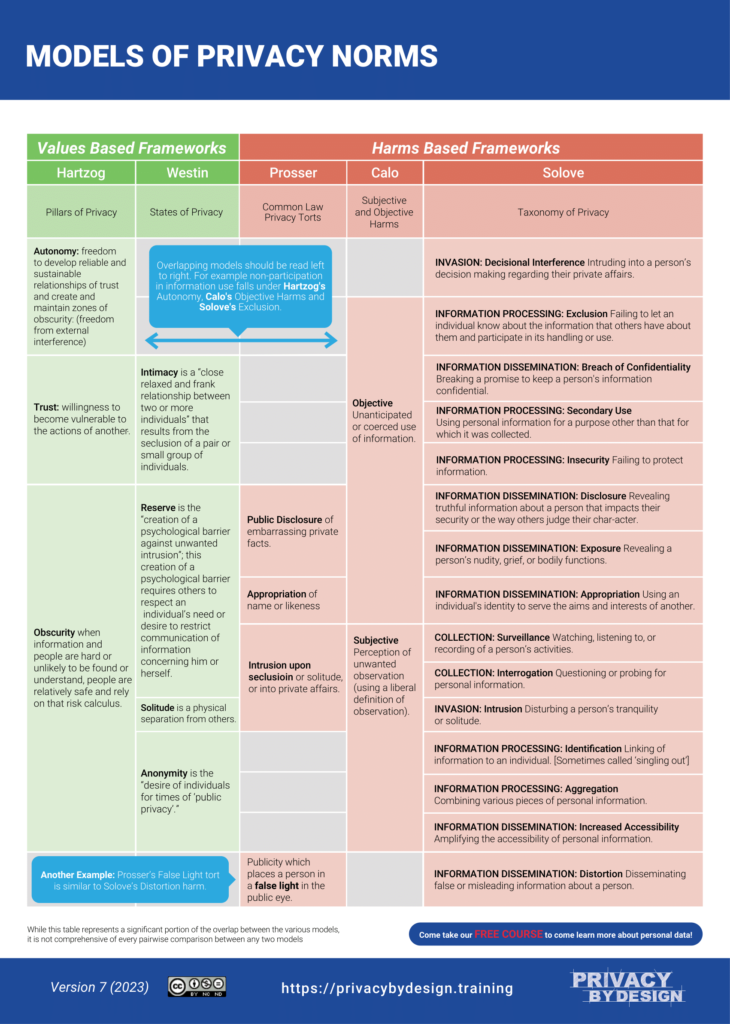
All infographics are CC BY and you may use them in their existing format. You may also download the original pdf here. For commercial use, please contact us. Download PDF
Categories of Personal Information Privacy Risk (Infographic)

All infographics are CC BY and you may use them in their existing format. You may also download the original pdf here. For commercial use, please contact us. Download PDF
NIST Privacy Framework: Assessments and GAP Analysis

Third party assessments help an organization gauge how they are doing and what they can be doing better. Many companies, leveraging the reputation of NIST, want an assessment against the Privacy Framework. But the framework is not a conformance standard, as many people mistakenly believe. Types of Assessments Assessment Type If your organization… Question Answered […]
NIST Privacy Framework Implementation: 5 Steps to Success

Begin with the End in Mind The NIST Privacy Framework is a tool for managing risk. In order to manage risk, you must first understand risk. This first step entails understanding the business, its operations, the clients, customers, vendors, partners and others it interacts with and most importantly, what it values and, in some cases, […]
Evaluate Your Privacy Program’s Maturity

It’s Not Only What You Do That Matters, But How Well You Do It Modern privacy programs have grown increasingly complex and, as a result, are less likely to operate as smoothly as intended. You may have a thorough privacy program in place, but how well does it actually function? This is the question that […]
Privacy Threat Modeling
Anticipate Risks Through Comprehensive Privacy Threat Modeling What You Don’t Know Can Hurt You The only way to reliably guard against privacy risks is to use a systematic approach to uncover and address these risks wherever they may be found in your company’s product, service, or process. This approach is called Privacy Threat Modeling, and […]
